Emelje és csökkentse a felhasználói jogosultság szintjét, és kezelje ezek felhasználói igényeit.
Automatikusan, menet közben, teljes naplózással.

Vészüzemmód, melyben teljesen megbízhat
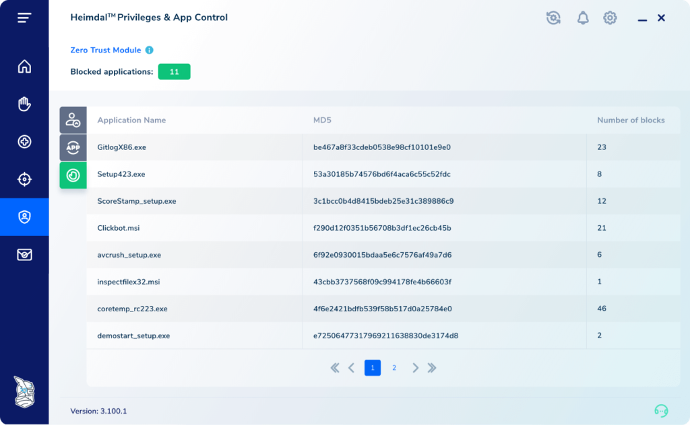
Nem számít mi történik az emelt szintű munkamenet során, a rendszer folyamatosan figyel az Ön biztonságára. Ez az egyetlen Privileged Access Management megoldás, amely automatikusan leállítja a felhasználói munkamenetet, amikor fenyegetést észlel a felhasználó eszközén.

Kapcsolja be a robotpilótát
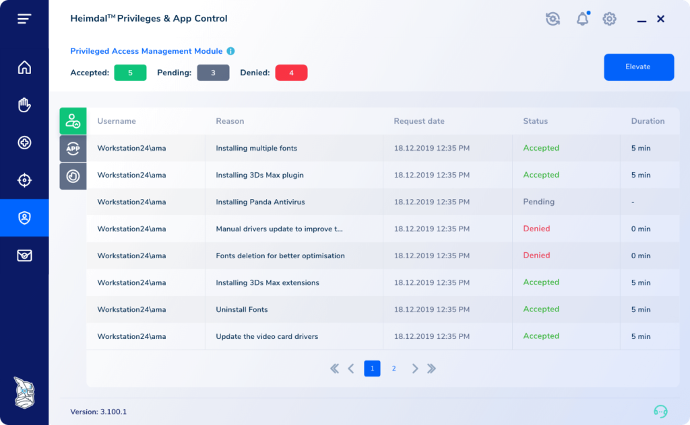
Megnövekedett mobilitás, a kérések jóváhagyásával vagy elutasításával töltött idő jelentősen csökken. Emelje és csökkentse a felhasználói jogosultságot a mobiltelefonjáról, bárhonnan a világból! Vegye át az irányítást a saját PAM felülete felett, hogy jóváhagyási vagy elutasítási folyamatokat hozzon létre, egyéni jogosultságokat állítson be AD csoportonként és eszkalációs időszakonként, távolítson el meglévő, helyi rendszergazdai jogokat és más beállításokat!

Azonosítsa és távolítsa el a rejtett sebezhetőségeket
Tudta, hogy a PAM segíthet önnek az operációs rendszer és a webböngésző sebezhetőségeinek eltávolításában? A Privileged Access Management segítségével a Windows operációs rendszer sebezhetőségeinek 93%-a, az összes böngészőspecifikus sebezhetőség 100%-a kiküszöbölhető a meglévő rendszergazdai jogok elvételével.
FŐBB ELŐNYÖK
Egyedi megoldások összetett problémákra
Egyszerűség a javából
A Privileged Access Management könnyen kezelhető és lenyűgöző felülettel rendelkezik, amely teljes irányítást biztosít a felhasználó emeltszintű munkamenete felett. Hagyjon jóvá vagy utasítson el kérelmeket a dashboard–ról vagy útközben a mobil eszközéről! Kövesse nyomon a munkameneteket, blokkolja a rendszerfájlok emelt szintű futtatását, vonja vissza akár azonnal a felhasználói adminisztrátori jogokat, állítsa be a magasabb szintű munkamenet időtartamát, és azonnal állítsa le a rendszerfolyamatokat a munkamenet lejártával!
Fokozottabb biztonság
A belső fenyegetések egyre veszélyesebbek. Kezelje őket a saját feltételeivel, a rendelkezésre álló legjobb eszközök segítségével! A Privileged Access Management egy extra biztonsági réteget hoz létre, amely megakadályozza a rosszindulatú programok terjedését a hálózaton – a jogosultságok automatikus visszavonásával, amikor fenyegetést észlel egy magasabb jogosultsággal rendelkező gépen. Megelőzés, védelem, biztonság hálózaton belül és kívül.
Hatékony auditáló eszközök
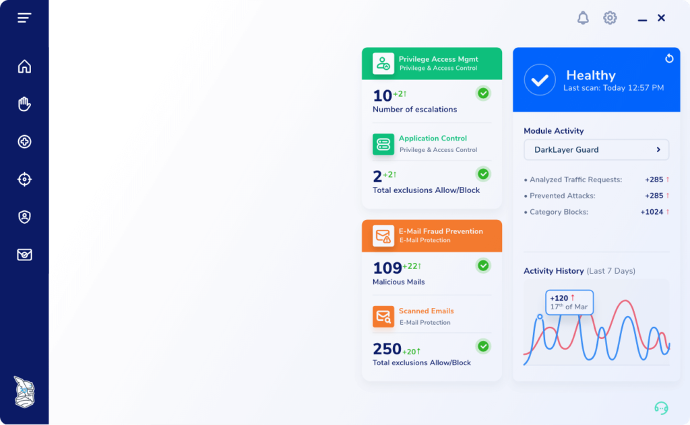
A biztonsági auditáló eszközök megnövelhetik vállalkozásának kiadásait. A Heimdal PAM fejlett adatelemzője segít kivizsgálni az incidenseket, és rendszeres biztonsági ellenőrzéseket végez. Pillanatok alatt biztosít grafikával teletűzdelt jelentéseket az érintett eszköz részleteiről, az eszkaláció átlagos időtartamáról, az eszkalált felhasználókról vagy fájlokról, az eszkaláció során futtatott fájlokról és így tovább.
Több mint a felhasználói jogok kezelése
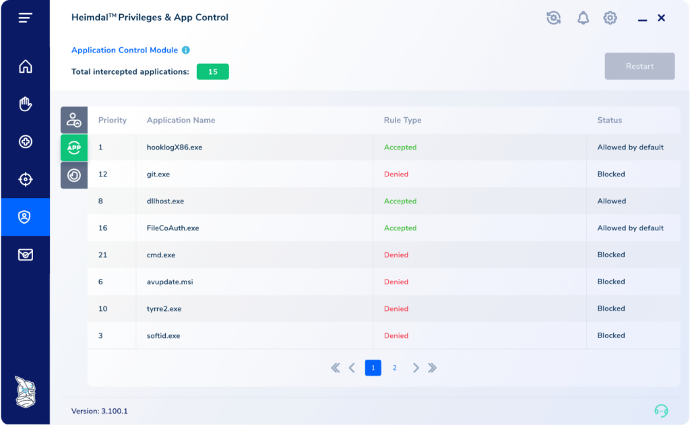
Lépjen túl a jogosultságok hozzáférésének kezelésén! A Heimdal segítségével könnyedén igazolhatja a NIST AC-5 és NIST AC-1,6 szabványok szerinti megfelelőséget, így ügyfelei és partnerei nyugodtabbak lehetnek. Kombinálja az Application Control modullal az alkalmazások, a felhasználók és a folyamatok szabályozására, vagy az újgenerációs vírusvédelemmel egy másodlagos biztonsági pajzs létrehozására. A lehetőségek tárháza végtelen. Készen áll a hozzáférések kezelésének jövőjére.
A globális cégek
kiberbiztonsági partnere
A Heimdal egyedülálló kiberbiztonsági megközelítéssel, egy olyan felületen, amely folyamatosan alkalmazkodik és fejlődik azáltal, hogy követi az IT bűnözőket és fejleszti az inkrementális intelligenciát, biztosítja néhány piacvezető vállalat jövőjét, hogy számukra a legfontosabbra, az üzletre koncentráljanak.

